


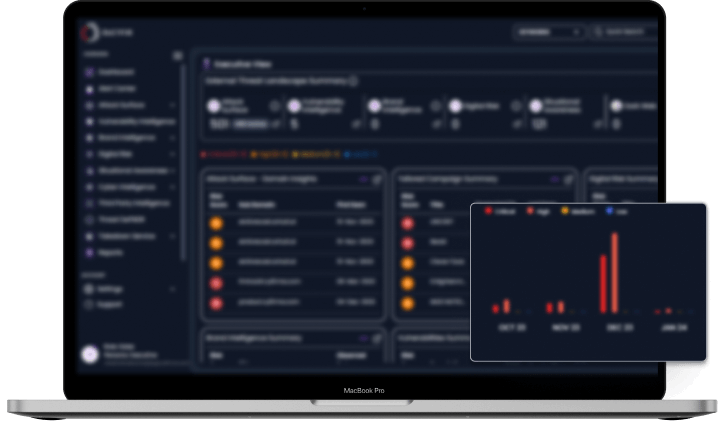
CYFIRMA’s ETLM model provides visibility across all parts of an organization, from risk management to IoC (indicators of compromise) ingestion in a multi-layered approach. This provides actionable insights at every level of the organization, from senior leadership to operation teams to facilitate key activities from strategic planning to tactical execution. Insights provided by CYFIRMA’s platform, are categorized into 3 key areas
Focuses on long-term implications for an organization. For instance, it provides the ability to effect change in a company’s risk registry and regulatory framework to ensure compliance.
Uncovers trends and approaches to support cybersecurity planning.
Allows teams to focus on tactics, techniques, and procedures (TTPs) of the adversary and examines IoCs to carry out immediate remediation steps and tactical execution.

More commonly, cyber intelligence solutions and services provide only tactical intelligence. However, ETLM allows organizations to gain insights across all three key categories of intelligence. This enables insights to be viewed in totality to enable an organization to make informed decisions and direct scarce cybersecurity resources to mitigate risk according to the severity of the threat.
The ETLM model follows the NIST framework and can be put into practice by both business and technology leaders.
The neuro-center of cyber-defense guides risk mitigation strategies and enables seamless integration into security toolsets to strengthen cyber posture.
Speak to CYFIRMA and start using the ETLM model to build your threat intelligence capabilities.
Get Started